How to Make Email Secure: Top Tips to Protect Your Account

Securing your email isn’t about finding a single magic bullet – it requires multiple layers of protection. Your inbox is the command center for your digital life, holding keys to your bank accounts, social media, and sensitive conversations. Leaving it poorly defended is an invitation for trouble.
Understanding the Pillars of Email Security
Email usage is massive and growing. We’re looking at a jump from roughly 4.83 billion global users in 2025 to nearly 523 billion daily emails by 2030. This volume makes email an irresistible target for attackers, which is why a solid security strategy is essential.
The Four Core Security Pillars
A truly secure email setup comes down to four key areas:
Authentication: Proving your identity with more than just a password – your first and most critical defense against account hijacking.
Threat Awareness: Training yourself to spot and sidestep scams, especially phishing emails designed to steal your credentials.
Encryption: Making your data unreadable by scrambling messages so intercepted information is useless without the decryption key.
Provider & Client Security: Choosing a secure email host and apps to access your mail. A weak foundation undermines everything else.
The biggest mistake people make is relying solely on a strong password. True email security is a system where each layer supports the others.
Building Your First Line of Defense With Strong Authentication

True digital security isn’t just about password complexity – it’s about building an authentication system that’s difficult for attackers but easy for you.
Ditch Traditional Passwords
Instead of hard-to-remember jumbles like Tr0ub4dor&3, use a passphrase – a sequence of random, unrelated words like correct-horse-battery-staple. Better yet, use a password manager to generate and store unique, complex passphrases for every service. You only remember one master password.
The Power of Multi-Factor Authentication
Even with a strong passphrase, you’re vulnerable if credentials get exposed in a breach. Multi-Factor Authentication (MFA or 2FA) is your secret weapon, adding a second layer that stops attackers even if they have your password.
MFA is the single most effective step you can take to secure your email. It neutralizes stolen passwords, which is how most accounts are compromised. Microsoft reports a 99.9% reduction in automated attacks with MFA enabled.
Security measures are making a difference. Projections show spam dropping from 48% of email traffic in 2025 to 43% by 2030, with phishing success rates plummeting from 0.12% to just 0.03%. You can dig deeper into these trends in cloudhq’s comprehensive email statistics report.
Choosing Your MFA Method
SMS Text Messages: Convenient but weakest due to SIM-swapping risks.
Authenticator Apps: Apps like Google Authenticator, Microsoft Authenticator, or Authy generate time-sensitive codes on your device. This is far more secure than SMS and should be the baseline for most people.
Physical Security Keys: Hardware devices like YubiKey offer the highest security and are practically immune to phishing.
How to Enable MFA on Popular Platforms
Getting MFA set up is a quick win—it usually takes less than five minutes. Here’s how you can get it done on the major email platforms:
Gmail: Head to your Google Account settings, click on the “Security” tab, and find the “2-Step Verification” section. From there, you can follow the prompts to add an authenticator app.
Outlook/Microsoft: Sign into your Microsoft account, choose “Security,” and then “Advanced security options.” You can enable two-step verification and add the Microsoft Authenticator app as your method.
Apple Mail/iCloud: On your iPhone or Mac, open System Settings, tap your name, then go to “Password & Security.” You’ll see the option to turn on Two-Factor Authentication right there.
How to Spot and Defeat Phishing Scams
Technical setups are only half the battle. The other half is learning to spot psychological tricks designed to make you act without thinking.
Phishing remains the number one inbox threat. In 2025, an estimated 3.4 billion phishing emails are sent daily. AI-driven phishing attempts have exploded by 4,000% since 2022, making them harder than ever to catch. You can dig into the specifics of this trend by reading the full research on phishing statistics at DeepStrike.io.
Deconstructing the Modern Phishing Attack
Modern phishing emails fake legitimacy and create urgency to force snap decisions. A common scenario: an email appears from Microsoft or your bank with official-looking logos and formatting, warning of a security alert or locked account that demands immediate action.
That’s the trap. Attackers count on panic to make you click before you think.
The core goal of any phishing email is to make you act on emotion rather than logic. Scammers know that when you’re worried or rushed, you’re far more likely to miss the subtle red flags that expose their con.
The infographic below really drives home the difference in risk and cost between secure and insecure email, highlighting why stopping these attacks is so crucial.
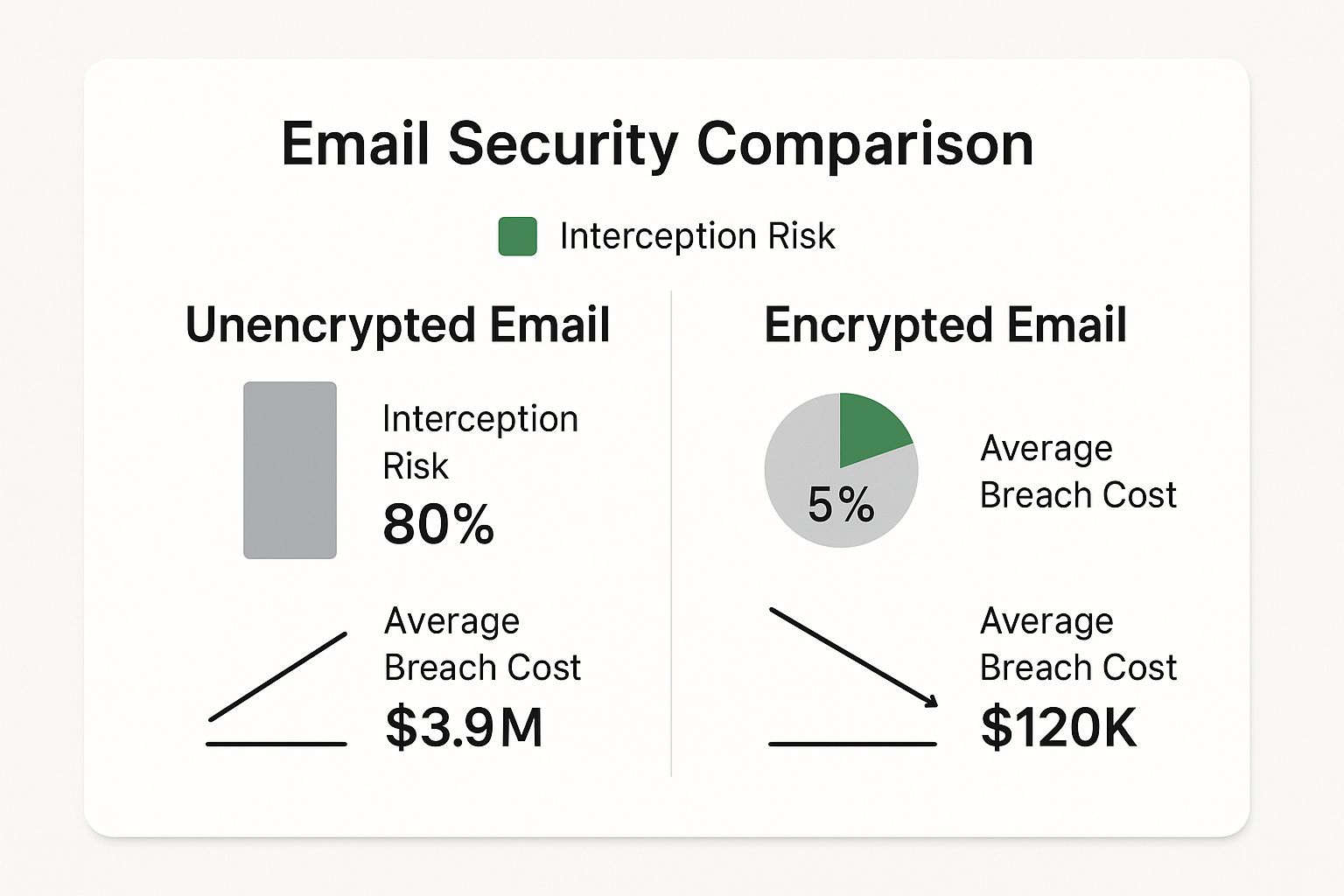
The data is clear. Encrypted, properly secured email dramatically cuts down both the chance of a successful attack and the financial damage if a breach does happen.
Evolving Threats: Quishing and Spear Phishing
Scammers never stand still. Two of the craftiest tactics gaining traction are “quishing” and AI-powered spear phishing. You need to have these on your radar.
- Quishing (QR Code Phishing): Emails contain QR codes instead of links. Security scanners check text and links, not images, so these slip past defenses. You scan the code and land on a fake login page.
- AI-Powered Spear Phishing: Scammers use AI to scrape your LinkedIn, company website, and social media, then craft highly targeted emails referencing your boss, recent projects, or conferences you attended.
These hyper-personalized attacks are tough to spot. For a deeper dive into real-world examples and what to do, check out our guide on how to identify phishing emails with expert tips.
Your Practical Phishing Detection Checklist
When an email feels off, stop and run through this checklist:
Examine the full sender address. Hover over the “From” field to see the real email address behind it. An official alert from Microsoft is never going to come from
microsoft.security@notice-123.net.Inspect links before you click. Hover over buttons or hyperlinks to see the true destination URL. If it looks weird or doesn’t match the sender, don’t click.
Analyze the tone. Is it trying to scare you? Demanding immediate action? Using generic greetings when companies usually use your name? Those are classic phishing tells.
Question every unexpected attachment. Never open attachments you didn’t request, even from people you know. Their account could be hacked.
Verify through a separate channel. Don’t use links in the email. Open a new browser tab, type the company’s website yourself, and log in there. Real notifications will be waiting.
Making this checklist a habit is how you go from being a potential target to being an active defender of your own inbox.
Using Email Encryption for True Privacy
Most standard email security works like a postcard – protected during transit but readable at the “postal hubs” (email servers). Transport Layer Security (TLS) is the default for Gmail and Outlook, stopping attackers from intercepting emails in transit. But your provider can still technically access message contents.
The Shift to End-to-End Encryption
For genuine privacy, you need End-to-End Encryption (E2EE). Your message locks on your device before sending and only unlocks for the intended recipient. Not even your email provider can read it.
This is essential for professionals in healthcare, finance, or law handling sensitive client data.
The core idea behind E2EE is simple: only the sender and the recipient hold the keys to unlock the message. It effectively removes the email provider from your circle of trust, ensuring your conversations remain completely private.
This isn’t just a “nice-to-have” in certain fields; it’s an absolute necessity. For professionals in healthcare, finance, or law, handling sensitive client data without this level of protection is a major risk. For a deep dive into specific industry requirements, our guide on HIPAA compliant email encryption explains what’s at stake.
Built-in Encryption Tools and Their Limits
The big email providers have noticed the growing demand for privacy and have rolled out their own “confidential” or “encrypted” modes. They’re a step in the right direction, but it’s vital to understand their limitations.
- Gmail’s Confidential Mode: Sets expiration dates and blocks forwarding, but Google still has access – it’s not true E2EE.
- Outlook’s Encrypt-Only: Restricts access to authenticated users, but Microsoft manages encryption keys and can technically access content.
These built-in options prevent casual snooping but don’t deliver absolute privacy.
| Feature | Best For | Key Limitation |
|---|---|---|
| TLS Encryption | Everyday, non-sensitive emails | Provider can access message content on their servers. |
| Gmail Confidential Mode | Preventing forwarding/printing | Not true E2EE; Google retains access to content. |
| Outlook Encrypt-Only | Restricting access to authenticated users | Not true E2EE; Microsoft manages the encryption keys. |
| True E2EE | Highly sensitive data (legal, financial, health) | Requires a dedicated service or tool for absolute privacy. |
When to Demand Absolute Privacy with E2EE
So, how do you decide what’s good enough? The answer comes down to the sensitivity of the information you’re sending.
Let’s get practical. Think about these real-world scenarios:
- Financial Records: You’re sending tax documents to your accountant, complete with your social security number and detailed financial history.
- Legal Matters: You’re discussing a confidential case with your attorney, where maintaining attorney-client privilege is non-negotiable.
- Business Strategy: You’re sharing proprietary trade secrets or M&A plans with fellow executives.
For these cases, use dedicated E2EE providers like Typewire or ProtonMail. These services are built on a “zero-access” architecture, meaning they are structurally incapable of accessing your data. Your privacy is guaranteed by design.
Advanced Email Infrastructure Security
Implement Email Authentication Protocols (DMARC, SPF, and DKIM)
If you manage a domain, implementing these three email authentication protocols significantly reduces spoofing and phishing attacks against your domain.
SPF (Sender Policy Framework): Publishes a list of authorized mail servers permitted to send emails on behalf of your domain, preventing attackers from forging your domain in the “from” address.
DKIM (DomainKeys Identified Mail): Adds a digital signature to outgoing emails, verifying that message content hasn’t been altered during transit.
DMARC (Domain-based Message Authentication, Reporting, and Conformance): Builds on SPF and DKIM by instructing receiving mail servers how to handle emails that fail authentication checks. You can set policies from “none” (monitoring) to “quarantine” or “reject.”
Benefits: PayPal reported a 70% reduction in fraudulent emails after implementing DMARC, while the U.S. Federal government achieved an 80% reduction in spoofing attempts.
Implementation tips:
- Start with monitoring mode (p=none) to identify all legitimate senders
- Implement SPF and DKIM before DMARC
- Gradually tighten policies from p=none to p=quarantine to p=reject
- Use third-party tools to analyze DMARC reports
Consider a Secure Email Gateway (SEG)
For organizations, a Secure Email Gateway acts as a vigilant gatekeeper, scanning all incoming and outgoing email traffic to intercept threats before they reach users.
What it does:
- Scans emails for malware, phishing URLs, and spam
- Tests suspicious attachments in a sandboxed environment
- Prevents data leaks through outgoing email inspection
- Provides centralized threat intelligence and reporting
When to use: Organizations handling sensitive data, operating in regulated industries, or facing frequent email-borne threats benefit most from SEG implementation.
Popular providers: Proofpoint, Mimecast, Cisco Secure Email, Barracuda Email Protection
Securing the Devices and Apps You Use for Email

Your email security is only as strong as its weakest link – often the device you’re using. A compromised device gives attackers a front-row seat to your digital life, making encryption and passwords useless.
Perform a Full Device Security Sweep
Run a full security sweep regularly. Nearly 60% of data breaches are linked to known but unpatched vulnerabilities.
Basic Checklist:
- Operating System: Make sure your Windows, macOS, Android, or iOS is set to update automatically. This is your device’s foundational defense.
- Browser and Extensions: Your browser is your main gateway to the web. Keep it updated and be ruthless—remove any extensions you don’t actively use or trust.
- Email Client: Whether you use the Outlook desktop app, Apple Mail, or something else, confirm it’s the latest version.
- Antivirus/Anti-Malware: Run a full scan with a reputable security program. Just as important, make sure its threat definitions are updated daily.
A common mistake I see is people focusing only on the operating system. Your browser and its extensions are just as critical. A forgotten, outdated browser extension can become a backdoor for an attacker to slip right through, completely bypassing all your other security efforts.
Audit and Revoke App Permissions
Over time, you’ve granted dozens of apps access to your email. Each connection is a potential security risk.
Go to your account’s security settings and find “Apps with access to your account.” For each app, ask:
- Do I still actively use this service?
- Does this app really need access to my email?
- Do I even recognize this company?
If the answer to any of these is “no,” revoke its access immediately.
Secure Your Network Connection
Finally, let’s talk about the network you’re using. Connecting to an unsecured public Wi-Fi at a café or airport can expose your traffic to anyone else on that network. While most email traffic is now encrypted in transit with TLS, a poorly configured network can still present serious risks.
At home, use a strong, unique Wi-Fi password (not the router default) with WPA3 or WPA2 encryption. This prevents unauthorized users from snooping on your network.
Apply the Principle of Least Privilege
The Principle of Least Privilege (PoLP) means granting users only the email access absolutely necessary for their job role. This minimizes damage from compromised accounts, insider threats, and data breaches.
How it works: Instead of blanket access to all email features, configure granular permissions for each user account based on job responsibilities. This might mean restricting access to shared mailboxes, limiting delegation rights, or tightly managing administrative privileges.
Benefits:
- Minimizes impact of compromised accounts
- Reduces insider threat risk
- Simplifies compliance with regulations
- Makes unauthorized activities easier to detect
Implementation tips:
- Audit current email permissions and remove unnecessary access
- Use role-based access controls (RBAC) rather than individual permissions
- Implement just-in-time access for administrative tasks
- Conduct quarterly access reviews with department managers
- Automatically revoke access when employees change roles or leave
Email Backup and Recovery
Losing access to emails due to accidental deletion, system crashes, or ransomware attacks can be devastating. Comprehensive email backup and recovery ensures you can restore data when primary systems fail.
Essential features of a backup solution:
- Automated, scheduled backups to eliminate human error
- Point-in-time recovery to restore to specific moments
- Immutable storage to protect backups from ransomware
- Granular recovery options (individual emails, folders, or entire mailboxes)
- Encryption of backup data both in transit and at rest
Why it matters: A law firm recovered seven years of critical client communications after a ransomware attack using immutable backups. A manufacturing company avoided paying a $2 million ransom by restoring from offline backups.
Best practices:
- Follow the 3-2-1 rule: 3 copies of data on 2 different media types, with 1 copy stored offsite
- Maintain air-gapped backups disconnected from production networks
- Regularly test recovery procedures with realistic scenarios
- Align retention policies with legal and compliance requirements
Popular solutions: Veeam Backup for Microsoft 365, Barracuda Email Backup, Druva inSync
Building Better Habits for Real-World Email Security
The best security tech can’t save you from a bad click. A 2025 analysis found that 95% of all data breaches were caused by human mistakes like sending emails to the wrong person. If you’re curious about the details, Mimecast’s State of Human Risk report is an eye-opening read.
Shrink Your Digital Footprint
Every bit of personal information you share online is a breadcrumb for attackers. Your birthday on Facebook, job title on LinkedIn, and city on Twitter help scammers craft convincing spear-phishing emails.
Review social media privacy settings and ask: “Does this need to be public?” Treat personal information like cash – that’s exactly what it is to scammers.
Compartmentalize Your Email Addresses
Stop using one email for everything. If one account gets compromised, the damage is contained.
Recommended setup:
- Primary Personal Email: For close friends and family only. Never for sign-ups.
- Financial & Admin Email: Exclusively for banking, bills, taxes, and sensitive correspondence.
- Public-Facing Email: For online shopping, newsletters, and non-critical sign-ups.
Adopt a “Zero-Trust” Mindset
Treat every email, link, and attachment as potentially hostile, no matter who it’s from. Even emails from colleagues or family could be threats if their account was hacked.
Before clicking, pause and ask:
- Was I expecting this?
- Does this request seem normal?
- Can I verify this through another channel (text or phone call)?
Frequently Asked Questions About Email Security
Is a VPN Enough to Secure My Email?
No. A VPN encrypts your internet connection, which protects you on public Wi-Fi, but offers zero protection if your email provider gets hacked or you click a phishing link. A VPN is valuable but not a complete solution.
Can I Trust My Email Provider’s Built-in Security?
For most people, yes. Google and Microsoft have powerful spam filters and TLS encryption. However, the single most important step is enabling Multi-Factor Authentication (MFA or 2FA) – even if a scammer steals your password, they can’t access your account without the second authentication factor.
For truly sensitive information, use end-to-end encryption services like Typewire or ProtonMail where not even your provider can read your messages.
How Often Should I Change My Password?
Forget the old 90-day rule. That leads to weak, predictable passwords. Instead, create unique, strong passphrases for each account and store them in a password manager. Only change passwords when you have specific reason to believe an account was compromised or a service announces a breach.
In passwords, strength and uniqueness beat frequency.
Ready to take control of your email privacy? Typewire offers secure, private email hosting built on a foundation of zero-access encryption. Say goodbye to ads and data mining, and protect your communications with a platform designed for true security. Explore our plans and start your free 7-day trial.
How to Make Email Secure: Top Tips to Protect Your Account
Posted: 2025-07-20
Best Secure Email App for iPhone in 2026
Posted: 2026-05-13
What Is PIPEDA Compliance for Your Business?
Posted: 2026-05-08
How to Create a Business Email That Protects Privacy
Posted: 2026-05-05
How to Send Large Video Files via Email Securely
Posted: 2026-05-02
Domain Name Expired: How to Secure Your Email and Business
Posted: 2026-04-29
Pros and Cons of Top Email Providers: A 2026 Privacy Guide
Posted: 2026-04-23
Electronic Mail Security: Guard Your Inbox Now
Posted: 2026-04-21
Typewire as a Private Email Alternative: 2026
Posted: 2026-04-17