How to Prevent Email Tracking: Your Complete Privacy Guide
Understanding What Email Tracking Really Means For You
Opening an email seems simple enough. However, a complex system of tracking mechanisms often operates behind the scenes. Email tracking has advanced far beyond simple read receipts. It now incorporates invisible pixels, link tracking, and behavioral analytics. These tools provide senders with a wealth of information about how you interact with their emails, effectively building a profile of your digital habits.
Embedded pixels, for example, are tiny, transparent images that load when you open an email. They can reveal when and how often you viewed the message, and even your approximate location. Clicking on links within the email offers further insights into your interests and online activity.
This collected data can then be used for a variety of purposes, such as creating targeted advertisements. It could even be used to influence your purchasing decisions. This constant monitoring can have a significant effect on your sense of privacy.
Knowing that your every email interaction is being scrutinized can be unsettling. It can create a sense of unease and diminish your feeling of online privacy. The potential for misuse of this data, or even unauthorized access, raises legitimate concerns.
The Evolving Regulatory Landscape
The regulatory environment surrounding email tracking is also changing. The evolving landscape of email security and privacy regulations is transforming how businesses handle email tracking. The rise of AI-driven scams and phishing attacks, which have increased by 28% in 2025, presents increasingly sophisticated email security threats.
New regulations, like the EU's DORA Regulation, effective in 2025, place greater responsibility on financial institutions to bolster cybersecurity surrounding third-party communications. This will impact how these organizations defend against Business Email Compromise (BEC) attacks. Learn more about email security threats.
Pixel-based tracking methods now risk being flagged with warnings visible to users. This is compelling marketers to rethink their strategies and adopt more transparent approaches. Understanding these tracking mechanisms is the first step towards taking back control of your inbox and protecting your digital privacy.
Your Legal Rights Against Invasive Email Tracking

You have significant power when it comes to your email privacy. This power comes from an evolving legal landscape designed to protect you from unwanted email tracking. This section explores key regulations that work to your advantage, helping you take back control of your inbox.
GDPR and CCPA: Setting the Standard
The General Data Protection Regulation (GDPR) and the California Consumer Privacy Act (CCPA) are important regulations in the fight against invasive tracking. The GDPR, implemented in the EU, mandates explicit consent for data collection, giving individuals greater control over their personal information. The CCPA provides similar protections for California residents, including the right to opt out of data collection and request the deletion of their data. These regulations have set a powerful precedent, influencing global privacy standards.
These landmark regulations have set a precedent for other regions and are shaping global privacy standards. The impact of these regulations is far-reaching, influencing how companies handle personal data worldwide.
Emerging State Privacy Laws and Real-World Victories
Beyond the GDPR and CCPA, numerous state-level privacy laws are emerging across the United States. These laws provide additional layers of protection for individuals, creating a complex but increasingly protective legal framework. Some of these laws grant consumers the right to know what data is collected, why it’s collected, and who it’s shared with. This transparency allows individuals to make informed decisions about their online privacy.
These legal frameworks have real-world implications for companies engaging in unauthorized tracking. Individuals are successfully challenging these practices in court, securing significant victories for email privacy. These cases underscore the importance of legal action in protecting online privacy and encourage further privacy enhancements.
Regulatory Developments and Impact
Regulatory bodies are also taking significant steps to enhance email security. For instance, the U.S. government is mandating phishing-resistant multi-factor authentication (MFA) adoption for email and critical systems by 2024-2025. This measure aims to combat Business Email Compromise (BEC) attacks, which accounted for 73% of reported cyber incidents in 2024.
The EU's NIS2 Directive further strengthens cybersecurity by requiring organizations to report significant cybersecurity incidents within 24 hours. Non-compliance can result in substantial fines up to €10 million. For more detailed statistics on BEC attacks and cyber incidents, see: Business Email Compromise Statistics.
Exercising Your Rights: Taking Action
These evolving regulations provide you with tools to protect your email privacy. You can demand transparency from companies regarding their tracking practices. Ask what data they collect, how it’s used, and who it’s shared with. You also have the right to request the deletion of your data and hold companies accountable for privacy violations.
By understanding and exercising your rights, you can take proactive steps to prevent email tracking and safeguard your online privacy. You can navigate the digital landscape with confidence, knowing you have legal avenues to protect yourself.
Bulletproof Email Client Settings That Actually Work

Your email client is your first defense against unwanted tracking. Many users stick with default settings, unknowingly compromising their privacy. Fortunately, a few key adjustments can significantly bolster your email security without disrupting your daily workflow.
Image Blocking: Your Primary Weapon
One highly effective method for preventing email tracking is blocking automatic image loading. This simple step prevents hidden tracking pixels from transmitting data when you open an email. Most email clients offer this feature, typically found within the privacy or security settings. In Gmail, for example, look for the "Ask before displaying external images" option.
This small change significantly reduces the information trackers gather about your email habits. Senders won't know when or how often you've opened their messages, giving you a powerful layer of protection against unseen surveillance.
Link Tracking: Understanding the Risks
Many email tracking techniques involve manipulating links to include unique identifiers. While completely avoiding links is impractical, understanding their potential for tracking is crucial. Be wary of shortened links or those containing unusual characters, as these can obscure the real destination and potentially redirect you to tracking websites.
A good practice is to hover your cursor over a link before clicking. This reveals the actual URL. If it differs from the link displayed in the email, exercise caution. This simple precaution helps avoid clicking potentially harmful or tracking-laden links, underscoring the importance of vigilance in online privacy.
Privacy-Focused Email Providers: Taking the Next Step
For those truly committed to email privacy, consider switching to a privacy-focused email provider like Typewire. These providers prioritize user privacy and offer features designed to thwart email tracking. Typewire, for instance, uses privately owned data centers and avoids third-party cloud providers to maximize data security.
Furthermore, email tracking prevention is gaining importance due to evolving privacy regulations. Apple's Mail Privacy Protection (MPP), introduced in 2021, significantly changed email tracking. MPP prevents senders from knowing if an email has been opened. This shift has led marketers to focus on conversion rates rather than open rates. Current retail and e-commerce conversion rates are benchmarked at 3.2-4.5%. Explore this topic further. This demonstrates the growing emphasis on email privacy.
Game-Changing Tools for Complete Email Privacy
Beyond adjusting your email client’s settings, specialized tools can significantly enhance your email privacy. These tools range from simple browser extensions to advanced privacy services and can provide a robust defense against email tracking.
Browser Extensions: Blocking Trackers at the Source
Several browser extensions actively block tracking attempts within your emails. Popular options like PixelBlock, Ghostery, and Privacy Badger offer varying levels of protection and features. PixelBlock, as the name suggests, specifically targets tracking pixels, preventing them from loading and transmitting data.
Ghostery takes a broader approach, blocking a wide range of trackers, including those used for advertising and analytics. Ghostery offers more comprehensive protection across various online activities. Privacy Badger, on the other hand, learns over time which websites and services are tracking you and automatically blocks their trackers. Privacy Badger provides a dynamic and evolving approach to tracker blocking.
- PixelBlock: Focuses specifically on blocking tracking pixels. PixelBlock is a targeted solution for pixel-based tracking.
- Ghostery: Blocks various trackers, including those used for advertising.
- Privacy Badger: Learns and automatically blocks trackers from websites that track you.
Choosing the right extension depends on your specific needs and preferences. Some users prioritize simplicity, while others seek maximum protection. Consider your technical comfort level and desired level of control when selecting an extension.
Advanced Privacy Services: Stripping Trackers Before They Reach You
For even greater control over email tracking, consider dedicated privacy services. These services act as intermediaries, filtering your emails before they reach your inbox. They strip out tracking pixels and other tracking elements, ensuring you receive clean, privacy-respecting messages.
Some services even offer features like email aliasing, allowing you to create unique email addresses for different websites. This further protects your identity and reduces unwanted tracking. Email aliasing adds an extra layer of anonymity and control over your online communications.
Privacy-Focused Email Providers: Built-In Protection
Another powerful approach to email privacy is choosing an email provider that prioritizes user protection. Privacy-focused email services like Typewire offer built-in tracking protection as a core feature.
They avoid using third-party cloud providers, keeping your data secure within privately owned data centers. Typewire's approach to user management and data control ensures that your data isn’t mined or used for targeted advertising. This provides a higher level of confidence in the security and privacy of your email communications.
The following infographic visualizes key data related to built-in tracker blocking in major email clients. It shows the percentage of clients offering the feature, the average number of trackers blocked monthly, and the percentage of users actively using it.
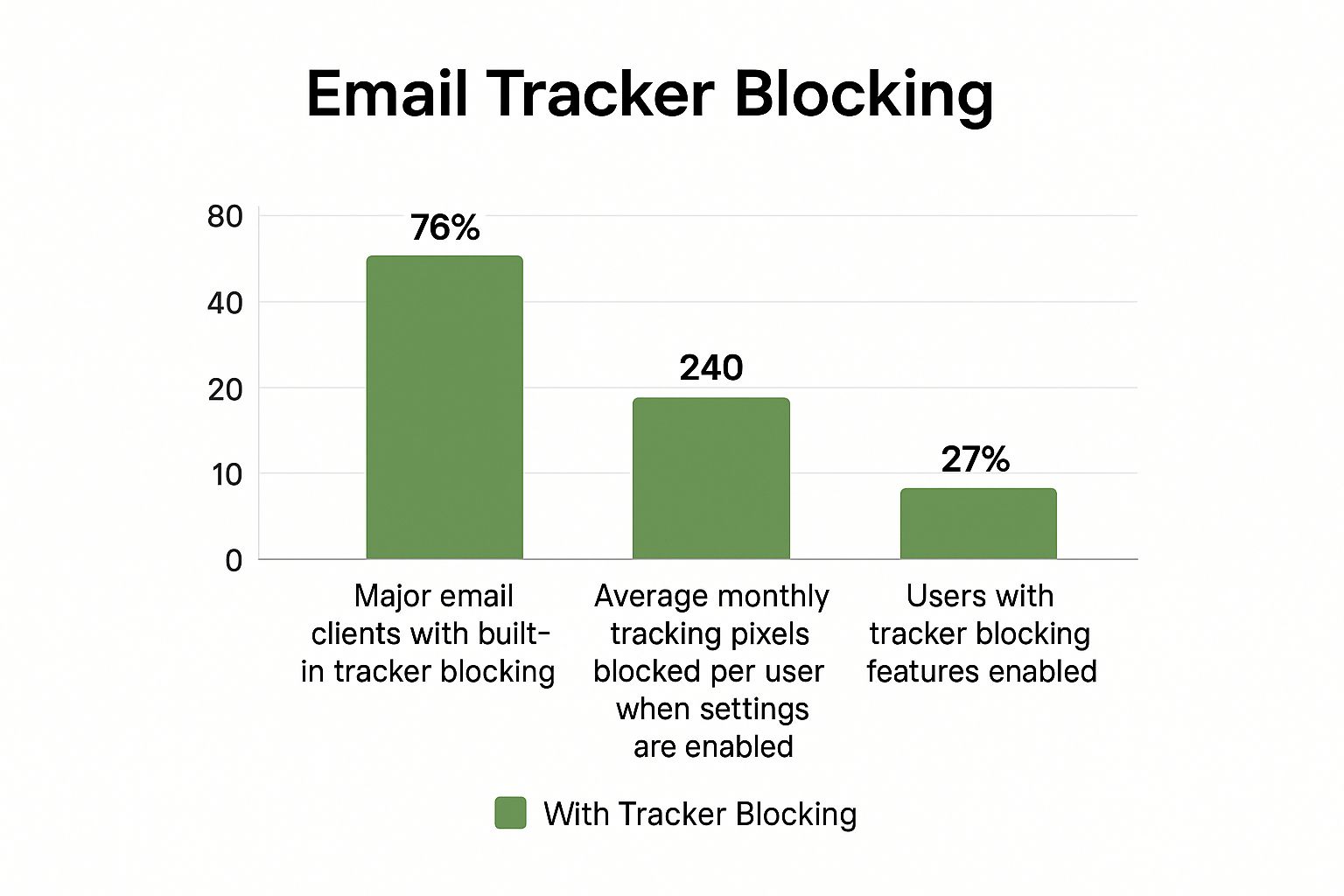
The infographic reveals a significant gap between the availability of tracker blocking features and their actual usage. While a substantial percentage of email clients offer some form of tracker blocking, relatively few users actively utilize these protections. This emphasizes the need for increased awareness and education about email privacy tools.
Finding The Right Tool For You
Implementing these tools can dramatically improve your email privacy. Whether you choose a browser extension, an advanced privacy service, or a privacy-focused email provider, the key is to find a solution that fits your needs and technical comfort level.
Understanding how to prevent email tracking empowers you to reclaim control over your inbox and protect your digital privacy. Taking proactive steps to enhance your email privacy can significantly reduce unwanted tracking and protect your personal information.
The following table provides a comparison of some popular email privacy tools:
Email Privacy Tools Comparison
A comprehensive comparison of popular email tracking protection tools, their features, compatibility, and effectiveness ratings.
| Tool Name | Type | Platform Support | Key Features | Effectiveness Rating |
|---|---|---|---|---|
| PixelBlock | Browser Extension | Chrome, Firefox, Edge | Blocks tracking pixels | High |
| Ghostery | Browser Extension | Chrome, Firefox, Safari, Edge | Blocks various trackers, including advertising and analytics trackers | High |
| Privacy Badger | Browser Extension | Chrome, Firefox, Edge | Learns and automatically blocks trackers | Medium |
| Typewire | Email Provider | Web, Mobile Apps | Built-in tracking protection, end-to-end encryption | High |
| SimpleLogin | Email Aliasing Service | Web, Browser Extensions | Creates unique email aliases for different websites | High |
This table highlights the variety of tools available, catering to different needs and technical skills. From simple browser extensions to comprehensive email providers, there are options for everyone seeking to enhance their email privacy. Consider your preferred platform, desired features, and level of technical expertise when selecting a tool.
Advanced Privacy Techniques for Maximum Protection
Taking control of your email privacy involves more than just adjusting basic settings. This section explores advanced techniques employed by privacy experts to thwart email tracking and achieve maximum protection. These strategies combine tools and best practices to build a strong defense against unwanted surveillance.
Email Aliasing: Creating a Wall Between You and Trackers
Email aliasing is a powerful method for creating multiple email addresses linked to your main inbox. This allows you to use a unique alias for each website or online service you use, establishing a barrier between your actual email address and potential trackers. If an alias starts receiving unwanted tracked emails, you can simply disable or delete it. This effectively stops the tracking without impacting your primary inbox.
This method offers significant control and anonymity, preventing companies from compiling a detailed profile of your online activity. Think of it like having a different phone number for each business contact, stopping them from cross-referencing your personal information.
Encrypted Email Providers: Securing Your Communications
Encrypted email providers represent a fundamental change in how your emails are handled. Unlike standard email services, encrypted providers scramble your messages, making them unreadable to anyone other than the intended recipient. This encryption shields your emails from prying eyes, even if they are intercepted in transit. This is especially crucial for sensitive communications or when sharing confidential information.
Typewire, for example, uses privately owned data centers, further reinforcing security and privacy. By avoiding third-party cloud providers, Typewire ensures your data stays under your control. This minimizes the risks of data breaches and unauthorized access.
Advanced VPN Setups: Masking Your Digital Footprint
While a basic VPN can conceal your IP address, advanced configurations offer even greater protection. Setting up a VPN on your router encrypts all internet traffic leaving your home network. This protects every device connected to your Wi-Fi, including smart devices that may not have individual VPN capabilities. Using a VPN with multi-hop functionality routes your traffic through several servers in different locations.
This added obfuscation makes it significantly harder to trace your online activity. Imagine sending a letter through several intermediaries; each forwarding step obscures the original sender.
Email Forwarding Chains and Proxy Services: Breaking the Tracking Chain
Email forwarding chains provide another powerful technique. This involves setting up multiple email addresses that forward messages to each other, ultimately reaching your main inbox. This breaks the direct connection between the sender and your primary email, disrupting tracking that relies on unique identifiers within links.
Proxy services can also boost your privacy. Proxies act as intermediaries between your device and the internet, masking your IP address and other identifying details. Using different proxy servers for various online activities further compartmentalizes your digital footprint, making it much harder to construct a complete picture of your online behavior.
Analyzing Email Headers: Identifying Hidden Tracking Elements
For a more in-depth understanding of email tracking, learn to analyze email headers. Headers contain detailed information about an email's journey from the sender to your inbox. Examining these headers can reveal potential tracking elements, such as hidden pixels or specially crafted links, exposing sophisticated tracking attempts not visible in the email body.
Testing and Verification: Ensuring Your Protection Works
Implementing these advanced techniques is only beneficial if they function correctly. Regularly test your setup to confirm its effectiveness. Send test emails containing known tracking elements and check whether your tools and configurations successfully block them. This ensures your privacy protection remains robust and adaptable to evolving tracking methods.
Building Your Personal Email Privacy Strategy
Effective email privacy isn't about using every single tool available. It's about finding a smart, sustainable approach that integrates seamlessly with your life. This means evaluating your individual needs and developing a personalized privacy strategy.
Assessing Your Vulnerabilities: Knowing Your Risks
Understanding your specific vulnerabilities is the first step. What kind of information do you regularly share via email? Are your concerns focused on targeted advertising, or more serious threats like identity theft? Understanding your risk profile is key to choosing the right protections.
For example, a journalist dealing with confidential sources will need a different level of security than someone primarily using email for online shopping.
Prioritizing Protections: Balancing Privacy and Productivity
Email privacy tools offer varying degrees of protection. Some offer basic protection against tracking pixels, while others provide robust encryption and anonymity. It’s crucial to balance your privacy needs with your daily workflow.
Implementing highly secure solutions can sometimes have an impact on productivity. If you depend heavily on email for work, select tools that integrate smoothly with your existing systems. This is where a personalized strategy becomes essential.
Layered Defense: Building a Stronger System Over Time
Think of email privacy like building a secure house. You wouldn't just rely on a locked front door. A multi-layered approach to email privacy is the most effective.
This might involve a combination of adjusting email client settings, using browser extensions, and possibly even switching to a privacy-focused email provider like Typewire. Every layer adds an additional barrier against tracking, building a more robust defense. Regularly reviewing and updating your strategy is vital, too, as online threats and email tracking methods constantly evolve.
Adapting and Maintaining Your Strategy: Staying Ahead of the Curve
Just as your life changes, so too might your privacy needs. A new job, relocating to a new country, or even changes in your online habits can all influence your risk level.
Regularly reassess your vulnerabilities and adjust your privacy settings accordingly. This ensures your protection remains relevant and effective.
Practical Frameworks and Timelines: Making It Manageable
Building an email privacy strategy doesn't have to be complicated. Break the process down into manageable steps. Start with simple protections like image blocking in your email client. Then, gradually explore browser extensions and other tools as needed.
Realistic timelines and step-by-step implementation make building a personalized strategy achievable. The following table provides personalized privacy strategies based on different user types.
To help you understand different approaches, the table below details customized privacy protection recommendations based on different user needs and technical expertise levels.
Email Privacy Strategy by User Type
| User Type | Priority Protections | Recommended Tools | Time Investment | Privacy Level |
|---|---|---|---|---|
| Casual User | Image blocking, Link awareness | Email client settings | Low | Moderate |
| Business User | Image blocking, Anti-tracking browser extension | Email client settings, PixelBlock, Ghostery | Medium | High |
| Privacy Advocate | Encrypted email provider, Email aliasing, VPN | Typewire, SimpleLogin, ProtonVPN | High | Maximum |
This table illustrates how different user types can prioritize their email privacy based on their individual needs and technical comfort level. It emphasizes that a personalized approach is key.
Protecting your email privacy is an ongoing process. By using a personalized, layered approach, you gain greater control over your digital footprint and protect your personal information.
Ready to take control of your email privacy? Start your free trial with Typewire today and experience the peace of mind that comes with secure, private email hosting. Explore Typewire now.
How to Prevent Email Tracking: Your Complete Privacy Guide
Posted: 2025-05-27
Best Secure Email App for iPhone in 2026
Posted: 2026-05-13
What Is PIPEDA Compliance for Your Business?
Posted: 2026-05-08
How to Create a Business Email That Protects Privacy
Posted: 2026-05-05
How to Send Large Video Files via Email Securely
Posted: 2026-05-02
Domain Name Expired: How to Secure Your Email and Business
Posted: 2026-04-29
Pros and Cons of Top Email Providers: A 2026 Privacy Guide
Posted: 2026-04-23
Electronic Mail Security: Guard Your Inbox Now
Posted: 2026-04-21
Typewire as a Private Email Alternative: 2026
Posted: 2026-04-17