Your Data Breach Response Plan for Hosted Email Security

Let’s get straight to it: a data breach response plan is your playbook for when your email security fails. It’s a formal document that lays out exactly who does what, what steps to take, and how to communicate when you suspect a security incident has hit your hosted email platform. The goal is simple: contain the threat, limit the damage, and get back to secure business communications as fast and cleanly as possible.
Why Your Email Platform Needs Its Own Response Plan

I’ve seen too many businesses rely on a general IT incident response plan, and frankly, it’s not enough. Your hosted email platform isn't just another application; it's the central nervous system for your entire business. It holds everything from sensitive client negotiations and financial data to intellectual property and personal employee information, making email privacy a top concern.
A generic plan just doesn't cut it because it fails to address the unique ways email can be exploited. An email breach isn't just about a compromised server—it's a direct pipeline into your company's most private conversations and data streams, shattering your email privacy guarantees.
The Unique Risks of Email Breaches
A standard response plan might be great for a lost laptop or a network intrusion, but it often falls short when dealing with threats specifically aimed at a hosted email environment. These attacks are crafty and designed to exploit human trust and the inherent openness of email, not just technical loopholes.
Here are a few threats that absolutely demand a specialized plan:
- Business Email Compromise (BEC): This is where attackers pose as executives or vendors to fool employees into sending money or sensitive files. Your general IT plan probably doesn't have a specific playbook for immediately verifying urgent financial requests or tracing these fraudulent email trails within your hosted platform.
- Rapid Account Takeovers: The moment an attacker gets into one mailbox, the clock is ticking. They can move sideways through your organization, reset passwords for other critical services, and use that trusted email account to phish your partners and customers. This is a direct assault on your email security.
- Cascading Data Exposure: A compromised inbox is a goldmine. Attackers can access years of attachments, full contact lists, and confidential conversations, turning a single breach into a massive data leak that violates email privacy on an epic scale.
A specialized data breach response plan for your hosted email is not just a "nice-to-have" IT document. It’s a core business strategy for protecting your most valuable communication channel, maintaining customer trust, and ensuring you can weather a direct attack.
Trying to figure this out in the middle of a crisis is a recipe for disaster. An email-focused plan gives your team a clear, step-by-step playbook for locking down accounts, warning users about specific phishing scams, and communicating with transparency.
To really build a strong foundation for your plan, it helps to understand the enemy. You can learn more about what you're up against in our complete defense guide to email security threats.
Building Your Dedicated Incident Response Team
A solid data breach response plan is a great start, but let's be honest—it’s just a document until you put the right people in charge of it. When a breach hits your email platform, you don’t have time for a frantic scramble to figure out who does what. What you need is a pre-defined Incident Response Team (IRT) that can jump into action immediately. This is what turns your plan from paper into a real, decisive strategy when the clock is ticking.
Without clear roles, people step on each other's toes, tasks get missed, and precious time is wasted. Having a team with a clear command structure eliminates that confusion from the get-go. This isn’t just about having bodies available; it's about empowering the right people with the authority to make critical calls on email security under pressure.
Defining Core Roles and Responsibilities
When you start building your team, think less about existing job titles and more about the essential functions you need covered. You need to handle the technical side of the email platform, the legal ramifications of a data privacy breach, and the communications—all at once. If you don't define who owns what, you're setting yourself up for failure.
Here’s a look at the essential roles you’ll want to establish:
- Incident Commander: This is your quarterback. They aren’t necessarily in the weeds fixing servers, but they direct the entire response, make the tough final decisions, and ensure the whole plan is actually being followed.
- Technical Lead (Email Security Specialist): This is your hands-on expert. They live inside your hosted email platform, digging through logs, identifying compromised accounts, and kicking the threat out of your systems for good.
- Communications Lead: This person manages every message going in or out. They’re responsible for keeping your own employees in the loop, crafting notifications for customers about potential email privacy violations, and handling any media inquiries to manage your reputation.
- Legal & Compliance Advisor: Data privacy laws are a minefield. This person is your guide, making sure you hit critical deadlines—like GDPR's 72-hour notification window—and protecting the organization from legal blowback.
With this structure, your tech lead can focus on email containment while your legal and communications leads work in parallel. It’s a much more efficient and less chaotic way to handle a crisis.
Before we dive deeper, it's helpful to see these roles laid out with their core duties and necessary skills. This isn't just a list; it's the blueprint for a team that can function seamlessly under extreme pressure.
Key Roles in an Email Incident Response Team
| Role Title | Primary Responsibilities During Breach | Essential Skills |
|---|---|---|
| Incident Commander | Oversees the entire response effort, coordinates team activities, makes final strategic decisions, and serves as the ultimate point of authority. | Leadership, calm under pressure, decisive decision-making, strong communication, project management. |
| Technical Lead | Leads the technical investigation, analyzes email logs and artifacts, identifies the breach's scope, and directs containment and eradication efforts within the email platform. | Deep expertise in email security protocols (SPF, DKIM, DMARC), log analysis, malware forensics, network security, knowledge of your hosted email platform. |
| Communications Lead | Manages all internal and external communications, drafts notifications for customers and stakeholders, and handles media relations. | Crisis communication, public relations, excellent writing skills, empathy, strategic messaging. |
| Legal & Compliance Advisor | Ensures all response activities comply with data privacy laws (GDPR, CCPA, etc.), advises on notification obligations, and manages legal risk related to email privacy. | Expertise in data privacy law, regulatory compliance, risk management, experience with breach notification requirements. |
This table gives you a clear starting point for assigning roles and identifying any skill gaps you might need to fill, whether through training or bringing in outside experts focused on email security.
Assembling Your Email Security A-Team
The exact size and makeup of your team will obviously depend on your organization, but these core functions are non-negotiable for email incident response. The most important thing you can do is assign these roles long before you ever need them. Make sure you have primary and secondary contacts for each role, because a crisis won't wait for someone to get back from vacation.
This level of preparation is more critical than ever. We're seeing attacks get smarter and more frequent, often targeting hosted email platforms directly. Phishing is still the king of initial access, kicking off as many as 95% of breaches involving human error. For a closer look at the numbers, you can explore current cybersecurity statistics to see what you're up against.
An Incident Response Team isn’t just a list of names on a document; it’s a living, breathing part of your security posture. Regular training and tabletop exercises focused on email threats are what build the muscle memory your team needs to perform calmly and effectively when a real crisis hits.
By taking the time to build and train this team now, you’re ensuring your organization can respond with confidence and control, not just react with panic.
Executing the Four Phases of Breach Response
When your hosted email environment is under attack, you don't have time for guesswork. A panicked scramble leads to mistakes. What you need is a clear, structured playbook that moves your team through the crisis with purpose and control.
We can break the entire process down into four distinct phases. Think of it as a framework that ensures every action, from the first hint of a compromised account to the final security patch on your email platform, is deliberate and effective. It's the difference between managing a crisis and being completely overwhelmed by it.
A critical part of this is having a defined response structure. You need clear lines of authority so everyone knows who to report to and who has the final say.
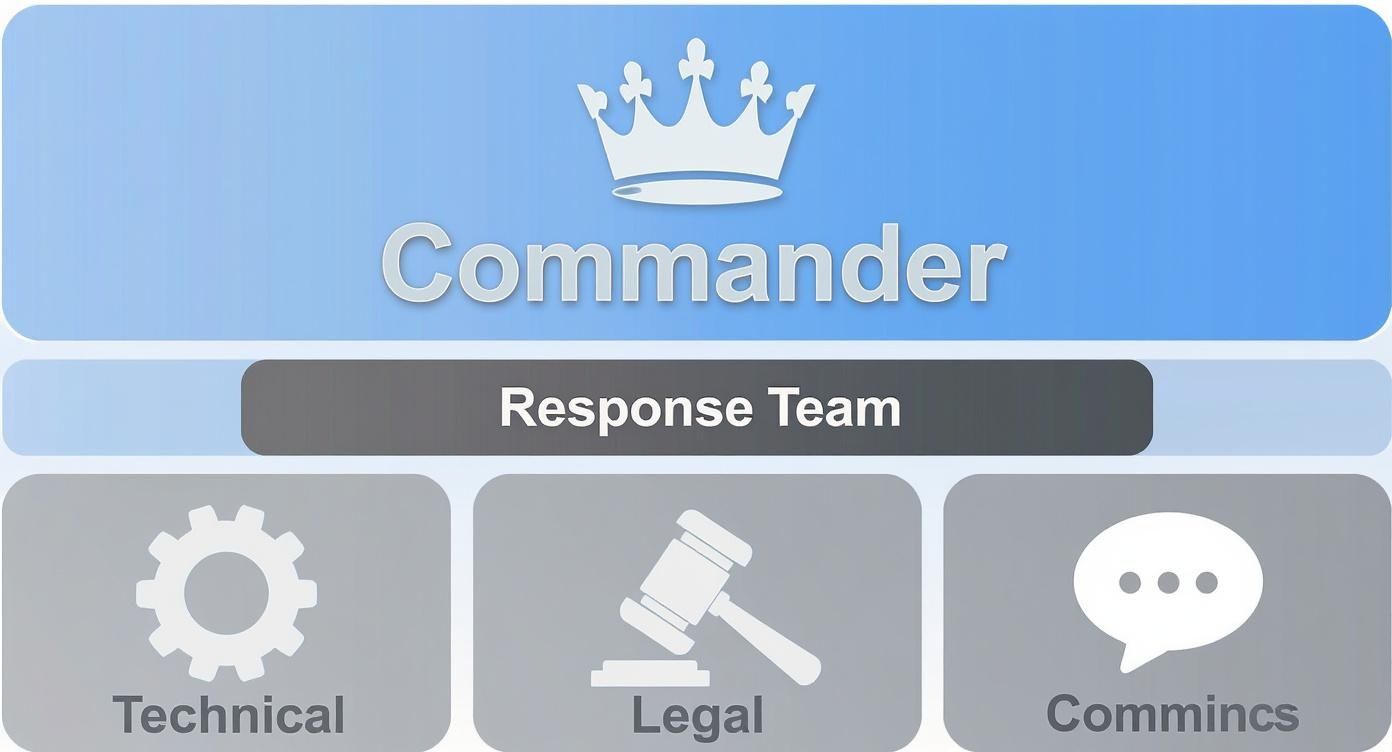
This kind of hierarchy prevents chaotic, siloed decision-making. While the technical, legal, and communication leads manage their own domains, the Incident Commander maintains overall strategic control of the email breach response.
Phase 1: Preparation and Proactive Defense
The best time to handle a data breach is long before it ever happens. This first phase is all about building your email security defenses and training your team so they can act decisively when a real threat shows up. It’s the foundation for everything that follows.
For a hosted email platform, this goes beyond just standard IT security. You have to focus on the unique vulnerabilities that come with email communication and user behavior.
Here’s where you should start:
- Run Tabletop Exercises: Don't just write a plan—pressure-test it. Simulate specific email threats, like a widespread phishing attack or a C-level account getting compromised. Walking your team through these scenarios is the best way to find communication gaps and weak spots in your procedures.
- Secure Your Configurations: Regularly audit your hosted email platform settings. Are you enforcing multi-factor authentication (MFA) for every single account? Have you reviewed user permissions to ensure no one has more access than they need? Have you implemented DMARC, SPF, and DKIM correctly to prevent spoofing?
- Develop Specific Playbooks: Create detailed, step-by-step guides for the most common email security incidents. You should have a playbook for isolating a compromised mailbox and a completely different one for handling a business email compromise (BEC) attempt.
Your goal in the preparation phase is to build muscle memory. When a breach hits, your team shouldn't be reading the plan for the first time. They should be executing a familiar set of actions with confidence.
Phase 2: Detection and Analysis
You can't fight an enemy you can't see. This phase is all about identifying an incident as quickly as possible and then figuring out exactly how bad it is. In an email environment, the early warning signs can be subtle and are easily missed if you're not looking for them.
Unusual login activity is a classic indicator. If a user account based in Vancouver suddenly logs in from a different continent at 3 AM, that's a massive red flag in your hosted email platform's logs. Another common sign is a sudden spike in outbound emails from a single account, which could mean a compromised mailbox is being used to blast out spam or malware.
Once you’ve detected a potential incident, the analysis has to be swift and thorough. Your technical team needs to find the answers to three key questions:
- Which accounts are affected? Is this an isolated user or a system-wide compromise of your email platform?
- What was the entry point? Did the attacker guess a weak password, or did they get in through a convincing phishing email?
- What data was accessed? The team needs to dig into the logs to see which emails, attachments, and contacts were viewed or, worse, downloaded, assessing the full scope of the email privacy violation.
The answers you find here will dictate the urgency and scale of your response. A single compromised account is serious, but an attacker with administrative access to your email platform is a five-alarm fire.
Phase 3: Containment, Eradication, and Recovery
Now we’re in the thick of it. This is the most active and intense phase of the response, where the primary objective is to stop the bleeding. You have to contain the threat, kick the attacker out for good, and get back to normal operations securely.
Containment is always your first move. This means isolating the affected parts of your email system to prevent any further damage.
- Immediately reset the passwords for all potentially compromised accounts.
- Temporarily suspend the accounts to completely block the attacker's access.
- Scrutinize email forwarding rules, as attackers often create them to exfiltrate data silently.
Next up is eradication. It’s not enough to just lock the door; you have to make sure the attacker and any tools they left behind are gone. This could mean removing malicious email forwarding rules, purging phishing emails from every user's inbox, and patching the vulnerability that let them in.
Finally, there's recovery. This is a careful, deliberate process—not just flipping a switch. You'll be restoring data from clean backups, closely monitoring the system for any sign of the attacker's return, and verifying that all your email security controls are working perfectly before you give users their access back.
Phase 4: Post-Incident Review and Improvement
The fire is out, but your job isn't done. The post-incident review is arguably the most important phase for your long-term email security. This is where you learn from what just happened to build a much stronger defense for the future.
This phase should start with a "no-blame" debrief with the entire response team. The goal is to get an honest assessment of what went well and where things fell apart. You need to ask some tough questions:
- Did our email security tools catch the incident fast enough?
- Were our communication channels clear and effective during the chaos?
- Did our containment procedures for compromised mailboxes actually work as we expected?
- Did this attack reveal gaps in our employee security training around phishing?
The answers should feed directly back into your data breach response plan, turning it from a static document into a living strategy that gets stronger with every challenge. The threat landscape is always changing. For example, recent events show a disturbing rise in supply chain attacks. In September 2025 alone, there were 49 publicly reported incidents with nearly 2 million confirmed breached records, but attacker claims suggest the true number could be over 1.5 billion due to a single major supply chain attack. You can learn more by reviewing a summary of recent global data breaches.
This makes it absolutely essential for your post-incident review to also consider third-party risks and insider threats to your email platform. Your plan has to be ready for anything.
Managing Communications During a Crisis

When an email data breach hits, the technical firefight is only half the battle. How you communicate is what will ultimately save—or sink—your reputation. A clear, empathetic, and timely communication strategy isn't an afterthought; it’s an essential pillar of your entire response plan.
Panic is the enemy of clarity. Without pre-approved messaging and a designated spokesperson, you risk sending mixed signals that just create more confusion and fear. The real goal here is to control the narrative by being the first and most reliable source of information about the breach of email privacy.
This means having a game plan for three very different audiences: your internal team, your customers, and the regulatory bodies breathing down your neck.
Notifying Your Internal Team First
Your employees should never, ever learn about a breach from the news or an angry customer. They are your front line and your best ambassadors during a crisis. Bringing them into the loop first equips them to handle incoming questions correctly and stops the rumor mill from spinning out of control.
Your initial internal memo needs to be direct and to the point. Make sure it covers:
- A brief, factual summary of the email security incident.
- The immediate steps being taken to contain the threat.
- Clear instructions on who handles external questions (hint: it's your Communications Lead).
- A quick reminder of their own data security responsibilities, such as reporting suspicious emails.
Keeping your team informed transforms them from anxious bystanders into a unified response unit. A team left in the dark can accidentally make things much, much worse.
Crafting Transparent Customer Notifications
This is where the stakes are highest. The way you notify affected customers has to be handled with care, absolute transparency, and a real sense of responsibility. Trust me, vague language or long delays will only make people angrier.
Keep the message simple and ditch the technical jargon. Be honest about what happened, what specific data was potentially exposed (e.g., email addresses and names, but not financial data), and what you're doing to improve email security. Most importantly, give them clear, actionable steps they can take to protect themselves, like watching out for phishing emails that often follow a breach.
A prompt and honest response can seriously limit the long-term damage. While the global average cost of a data breach thankfully dipped to $4.44 million in 2025—thanks largely to faster detection—the United States is still facing an average cost of $10.22 million per incident. These numbers aren't just statistics; they show how a well-communicated response has a direct financial impact. To get this right, it pays to understand what makes an effective crisis PR strategy.
Engaging With Regulatory Authorities
Depending on where you operate and the data involved, you probably have a legal duty to report the breach. Regulations like GDPR in Europe or CCPA in California have very strict notification windows. GDPR, for example, gives you just 72 hours from the moment you discover the breach.
Your response plan absolutely must have a section detailing these legal requirements related to email privacy. Work with your legal counsel to document and clarify:
- Who to notify: Which specific data protection authorities need a report?
- When to notify: What is the hard deadline you cannot miss?
- What to include: What specific information are you legally required to provide?
Missing these deadlines or sending an incomplete report can lead to massive fines. That's a legal and financial disaster piled on top of an already stressful technical one. Having this documented ahead of time removes the guesswork when the pressure is on.
Testing and Improving Your Response Plan
A data breach response plan that just sits on a server gathering digital dust is worse than having no plan at all. It gives you a completely false sense of security. For your plan to mean anything, it has to be a living document—something you’ve pressure-tested and know will actually work when things go sideways.
This isn't about checking a box for compliance. It's about building muscle memory for an email security crisis.
When a real email security incident hits, you want your team running a familiar playbook, not frantically searching for a document they’ve never opened. The only way to find the hidden cracks in your procedures and communication flows is to run regular drills.
From Tabletop Scenarios to Full-Scale Drills
Testing doesn’t always have to be a full-blown, panic-inducing simulated attack. The trick is to mix up the intensity and focus of your drills to challenge different parts of your plan and your team. This way, every aspect of your email breach response gets sharpened over time.
You can ramp up your efforts as you go:
- Tabletop Exercises: These are essentially guided war-gaming sessions. Get the response team in a room and walk them through a specific scenario, like a convincing business email compromise (BEC) attack that targets your finance department. Everyone talks through their exact roles and what they would do. It’s a low-stress way to uncover glaring gaps in your process.
- Walkthroughs: This is a step up. Instead of just talking about it, team members actually perform some of their assigned tasks. Maybe they draft a sample notification email or try to pull the specific logs from the hosted email platform needed for an investigation. This quickly reveals if your tools and templates are as accessible as you thought.
- Red-Team Drills: This is the ultimate test. You hire an external security team (the "red team") to actively try and break into your email environment. It’s an unfiltered, honest look at your real-world defenses and shows you exactly how your team performs under genuine pressure.
The most valuable part of any test isn't whether you "pass" or "fail." It's the brutally honest debrief afterward. Every drill has to end with a no-blame review to figure out what worked, what broke, and what needs to change.
Turning Lessons into Actionable Improvements
After every single test, you have to take what you learned and feed it directly back into your response plan.
Did the tech team have trouble isolating a compromised account in your hosted email platform? Your containment playbook needs more detailed, step-by-step instructions. Did it take the communications team hours to draft a simple customer update? Your pre-approved templates clearly aren't good enough.
This constant feedback loop is what separates a great plan from a useless one. It also forces you to look at your broader email security posture. A fantastic way to stay on top of this is by performing regular security audits. For a solid framework, you can follow a guide like our 7-point email security audit checklist.
Finally, remember that post-incident cleanup isn’t just about software patches. To truly harden your defenses, you have to think about the entire data lifecycle. This means implementing strict data disposal measures for old hardware, like using professional hard drive destruction services. It’s a simple step that ensures sensitive data from decommissioned systems can never be recovered, closing a common and often-forgotten vulnerability.
Frequently Asked Questions
When you're in the trenches building a data breach response plan, especially one focused on something as critical as email, a lot of practical questions pop up. Getting those questions answered is the key to creating a plan that actually works when the pressure is on. Here are some of the most common things we get asked by organizations working to protect their hosted email platforms.
We wanted to give you direct, no-nonsense answers that help clarify the tricky parts of testing, common mistakes we see people make, and why a separate plan for email is a non-negotiable in today's world.
How Often Should We Test Our Email Data Breach Response Plan?
Your plan is only as good as your team's ability to execute it under pressure. That’s why regular testing is so important. As a rule of thumb, you should be running tabletop exercises at least twice a year and a full-blown simulation annually. Think of it as building muscle memory for a crisis.
That said, don't just stick to a rigid calendar. Any major change should trigger an immediate test. Did you just migrate to a new hosted email platform? Reorganize the response team? Roll out a new security tool? Test the plan. You need to be sure your procedures still hold up.
This isn't a one-and-done deal. It's like a fire drill. You don't just run it once and hope everyone remembers what to do five years later. Practice turns a chaotic scramble into a coordinated, reflexive response.
What Is the Single Biggest Mistake Companies Make?
Without a doubt, the most damaging mistake we see is delayed communication. It happens all the time. A company hesitates to inform employees, stakeholders, or customers about an email breach, usually out of fear of causing a panic or because they're still gathering facts. But that delay is a killer for trust and email privacy.
Your response plan has to short-circuit this hesitation. By having pre-approved communication templates and a crystal-clear notification strategy ready to go, you remove the guesswork. The second a breach is confirmed, your communications lead should be adapting those templates and getting the word out. Being timely, transparent, and honest builds far more credibility than silence ever will.
Do We Need a Separate Plan for Email Security?
Yes. One hundred percent. A general IT incident response plan is a great starting point, but it's dangerously insufficient for the unique threats hammering hosted email platforms every single day. Email is still the number one way attackers get in, and you need a specialized playbook to counter them.
Think about it—your general IT plan probably doesn't have specific, step-by-step instructions for dealing with threats like:
- Business Email Compromise (BEC): What's the immediate playbook when an attacker spoofs the CEO's account to request a fraudulent wire transfer?
- Mass Account Compromise: How do you handle a situation where a phishing campaign has compromised 50, 100, or more user mailboxes at once?
- Credential Stuffing Attacks: What are the containment protocols when automated bots are hammering your login portals with stolen passwords?
A dedicated email data breach plan gives you the specific containment and remediation steps to shut down these kinds of attacks before they cause catastrophic damage to your business and your reputation for email privacy.
Who Should Have the Final Say During an Email Breach?
In a crisis, you need a single, clear source of authority. That person is the designated Incident Commander. They must have the final say on all critical decisions. This isn't about them micromanaging the technical team's every move; it's about maintaining a strategic, 10,000-foot view of the entire response.
The Incident Commander is the glue holding everything together. They coordinate the technical team's containment efforts, the legal team's compliance obligations, and the communications team's external messaging. This prevents the chaos of conflicting orders and allows each lead to execute their role confidently. Without that central decision-maker, even the best-laid plans can fall apart.
A well-rehearsed data breach response plan is an essential defense for your company's most vital communication tool. At Typewire, we've built a secure private email hosting platform with privacy and security baked in from the ground up, giving you the foundation you need to protect your data. Learn more about how Typewire can secure your business communications.
Your Data Breach Response Plan for Hosted Email Security
Posted: 2025-11-28
What Is CASL? Canada’s Anti-Spam Law, Explained
Posted: 2026-06-02
What Is Whaling? How Executive Email Fraud Works
Posted: 2026-05-29
What Is a Phishing Email Example: Spot Dangerous Scams 2026
Posted: 2026-05-26
What Is a Digital Signature? A 2026 Guide to Secure PKI
Posted: 2026-05-24
One Simple Email Privacy Habit Everyone Should Start Doing
Posted: 2026-05-17
Best Secure Email App for iPhone in 2026
Posted: 2026-05-13
What Is PIPEDA Compliance for Your Business?
Posted: 2026-05-08
How to Create a Business Email That Protects Privacy
Posted: 2026-05-05